- August 25, 2023
- Posted by: Bharat Dhyani
- Category: Data & Analytics

Data modernization strategies for improved fraud detection in banking involve leveraging advanced technologies and techniques to enhance the detection and prevention of fraudulent activities.
Here are some key strategies to consider:
1. Data Integration and Consolidation
Data integration and consolidation in the context of fraud detection in banking refers to the process of bringing together data from various sources within the bank’s ecosystem and merging it into a unified view. This unified view provides a comprehensive and holistic understanding of customer behavior, transactions, and other relevant data points that are crucial for effective fraud detection.
Data Sources: Banks have multiple data sources that generate valuable information for fraud detection. These sources include transaction logs, customer account data, credit card information, online banking activity, customer profiles, external data feeds (such as watchlists or blacklists), and more. Data integration includes addressing data inconsistencies, resolving data format issues, eliminating duplicates, and validating data accuracy.
To consolidate the data, banks often use data warehousing or data lakes.
Data Integration Techniques: These are employed to integrate data from various sources.
These techniques include Extract, Transform, and Load (ETL) processes.
This consolidated data serves as the foundation for implementing advanced analytics techniques, such as machine learning and behavioral analytics, to detect fraudulent patterns and anomalies effectively. It enables banks to identify suspicious activities, transactional patterns, and potential fraud indicators that may be missed when analyzing data from individual sources in isolation.
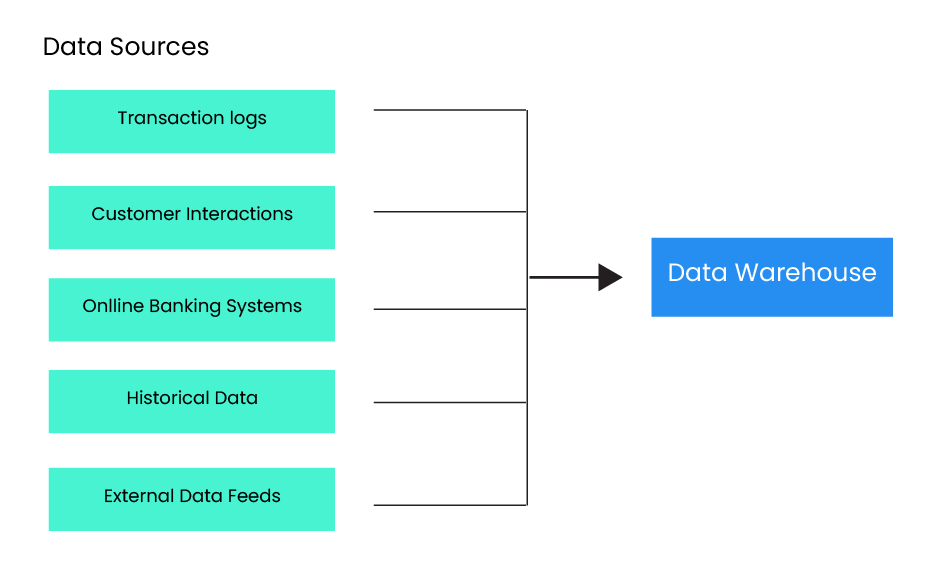
Figure 1 Data Consolidation from various data sources in Banking
2. Real-time Data Processing
Traditional batch processing may not be sufficient for timely fraud detection. Implementing real-time data processing capabilities allows banks to analyze transactions and customer data in near real-time, identifying potential fraud patterns as they occur. This enables immediate action to prevent fraudulent transactions.
Data from various sources, such as transaction logs, customer interactions, online banking systems, and external data feeds, is ingested in real-time or near real-time. This data is typically collected using technologies like messaging systems, event-driven architectures, or specialized streaming platforms.
As data is ingested, it undergoes processing and analysis in real time. This involves applying algorithms, models, and rules to detect anomalies, patterns, and indicators of fraudulent activities. Machine learning, artificial intelligence, and statistical analysis-like approaches are used to identify and score potential fraud in streaming data.
It allows for faster and more proactive fraud detection, enabling banks to stay ahead of emerging fraud patterns and protect customers and their financial interests.
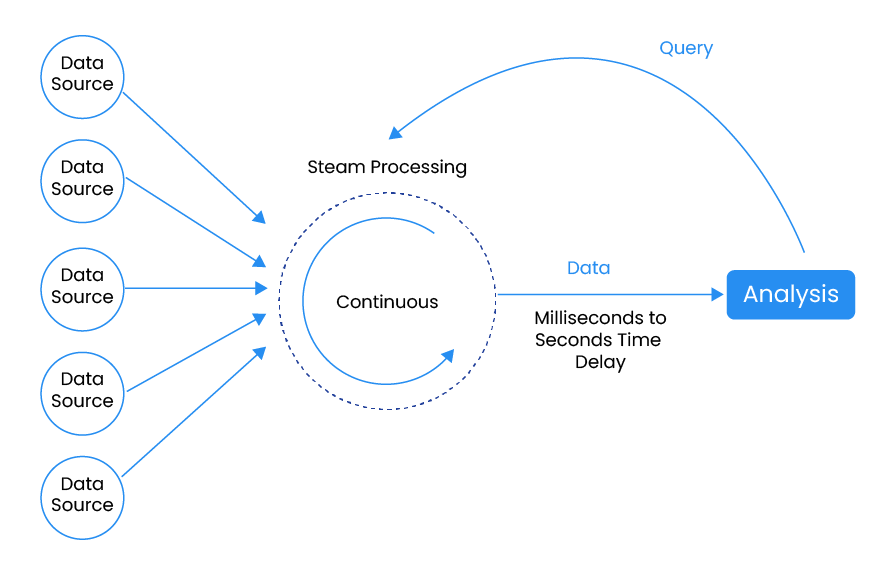
Figure 2 Real-Time Data Processing (Source: https://hevodata.com/learn/real-time-processing)
3. Machine Learning and AI
Artificial intelligence (AI) and machine learning (ML) techniques have excelled at enhancing fraud detection in the banking sector. To discover patterns of fraudulent behaviour and spot anomalies in real-time data, these models can be trained on historical data. Adapting models to changing fraud strategies requires constant model improvement and modification.
Feature Engineering: Feature engineering is a crucial step in ML for fraud detection. It involves selecting and transforming relevant data attributes or features that can contribute to accurate fraud detection. These features may include transaction amount, location, time, frequency, customer behavior, historical patterns, and more. Feature engineering helps capture meaningful patterns and improve the performance of ML models.
Supervised and Unsupervised Learning: ML techniques for fraud detection can be categorized into supervised and unsupervised learning approaches.
In supervised learning, models are trained using labeled data, where historical instances of fraud and legitimate transactions are identified. This enables the model to learn from past examples and make predictions on new data.
On the other hand, unsupervised learning is used for anomaly detection, where the model identifies patterns that deviate from normal behavior without needing labeled training data.
Predictive Models: ML algorithms, such as decision trees, random forests, support vector machines (SVM), or neural networks, can be utilized to build predictive models for fraud detection. These models learn from historical data and predict the likelihood of a transaction being fraudulent based on its features. Predictive models provide a risk score or probability that aids in prioritizing alerts and focusing investigation efforts on high-risk transactions.
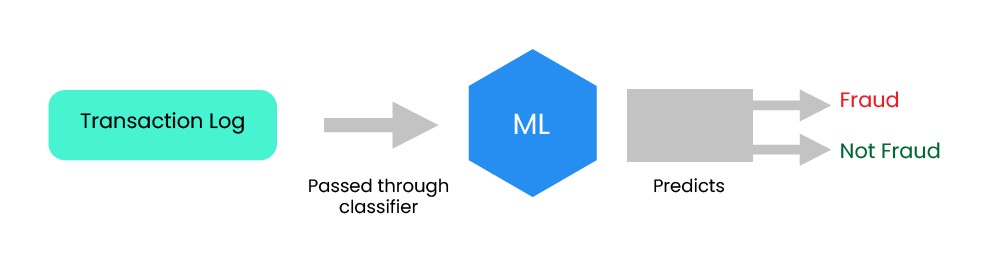
Figure 3 Model predicts whether the transaction is Fraud or Not Fraud.
Anomaly Detection: ML algorithms can be trained on historical data to learn patterns of normal customer behavior, transactional patterns, and typical account activities. By identifying deviations from these established patterns, ML models can flag transactions or activities that are likely to be fraudulent. Anomaly detection techniques, such as clustering, classification, and outlier detection, are applied to identify suspicious patterns that require further investigation.
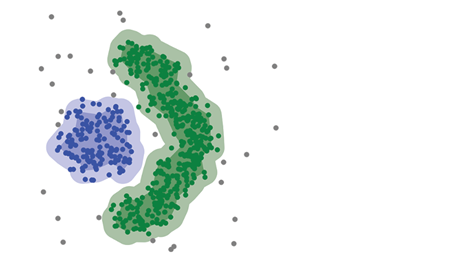
Figure 4: Example – Clustering of “Fraud” and “Not Fraud” data points
Continuous Model Training: Fraudsters constantly adapt their techniques, which makes it essential to continuously update and retrain ML models. By regularly feeding the models with new data and adjusting their parameters, banks can keep the models up to date and improve their accuracy in detecting new fraud patterns.
Behavioural Analytics: ML and AI algorithms are instrumental in analyzing customer behavior and identifying suspicious patterns. By establishing baseline behaviors for individual customers and monitoring deviations from those patterns, ML models can detect abnormal activities that may indicate fraudulent behavior. ML models can analyze various behavioral aspects, such as transaction amounts, frequency, location, device usage, spending patterns, and interactions across multiple channels.
Let’s consider a bank that wants to detect fraudulent credit card transactions using behavioral analytics. The bank collects data on customer transactions, including transaction amounts, merchant categories, transaction frequency, location, and time of day.
1. The first step is to establish baseline behavior for each customer. This baseline is created by analyzing their historical transaction data, such as average transaction amounts, typical merchant categories, and regular transaction frequencies. For example, if a customer typically makes small transactions at local retail stores during weekdays, this becomes their baseline behavior.
2. Once the baseline behavior is established, the bank continuously monitors customer transactions in real time. Any deviation from the baseline behavior is flagged as a potential fraud indicator.
For instance, if a customer suddenly starts making large transactions at high-risk merchant categories.
3. Each flagged transaction is assigned a risk score based on the degree of deviation from the customer’s baseline behavior. A higher risk score indicates a higher likelihood of fraud.
4. Transactions with high-risk scores trigger alerts for further investigation. These alerts can be sent to fraud analysts or automated systems for immediate action.
5. Behavioural analytics models continuously learn and adapt to new patterns and behaviors. As new data is collected and fraud patterns evolve, the models update their baselines and adjust the thresholds for detecting deviations. This adaptive learning helps improve the accuracy of fraud detection over time.
Network Analysis: ML techniques can be used to analyze complex networks of transactions, accounts, and relationships to identify fraudulent networks or syndicates. By uncovering hidden links, ML models can detect coordinated fraudulent activities that may involve multiple accounts or individuals working together to commit fraud.

Figure 5 Graph network structure of customers and their transactions, relationships, etc.
Example: Consider a bank that wants to detect fraud involving multiple accounts working together in a coordinated manner. The bank gathers relevant data, including customer account information, transaction records, and any known connections between accounts or individuals.
1. The first step is to visualize the network of customers and accounts. This can be done by representing each entity as a node and the relationships between them as edges. One example by which this can be done easily is DGraph by Google.
2. Network analysis techniques are applied to identify patterns or clusters within the network. These patterns can reveal relationships that may be indicative of fraudulent activities. For instance, clusters of accounts with shared addresses, and frequent transactions among a specific group of customers.
3. By comparing the observed network structure to expected patterns or baseline behaviors, unusual or unexpected relationships can be identified. For example, if a group of accounts suddenly starts transacting heavily with each other despite having no prior connections, it may indicate a coordinated fraud attempt.
4. Additional analysis can be performed like social network analysis (identify influential or central nodes within the network) or link analysis (trace and analyze the flow of funds or transactions within the network).
5. Based on the findings of network analysis, alerts can be generated for further investigation
Model Ensemble and Hybrid Approaches: Combining multiple ML models into an ensemble or using hybrid approaches that combine rule-based systems with ML techniques can improve fraud detection accuracy.
Ensemble models aggregate predictions from multiple models to make more robust and accurate decisions, while hybrid approaches leverage the strengths of both rule-based and ML systems to enhance fraud detection capabilities.
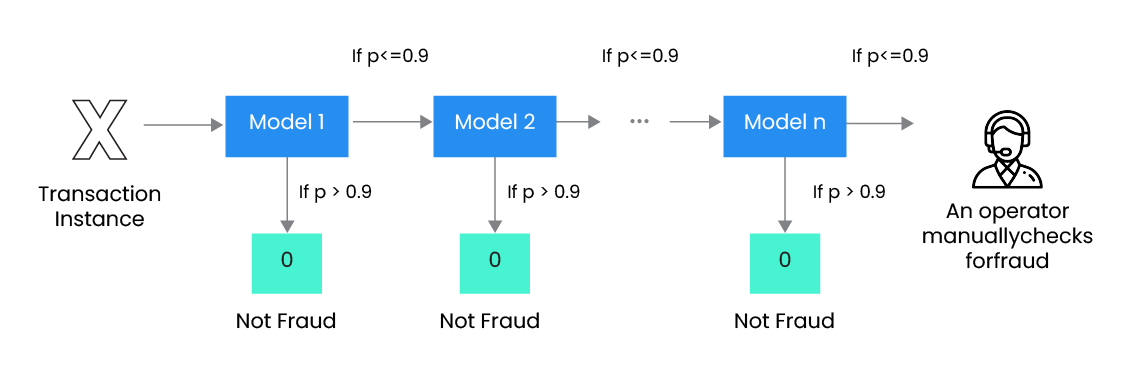
Figure 6: Cascading ensemble technique (Source: https://www.toptal.com/machine-learning/ensemble-methods-kaggle-machine-learn )
Explainability and Interpretability: Interpreting ML model decisions and providing explanations for fraud detection outcomes are important for regulatory compliance and transparency. Techniques such as feature importance analysis, model explainability algorithms, or rule extraction methods can help provide insights into the factors influencing model decisions and increase trust in the ML-based fraud detection system.
Human-in-the-Loop: While ML and AI play a significant role in automated fraud detection, human expertise, and intervention remain crucial. Human analysts play a critical role in investigating flagged cases and validating ML outputs.
4. Enhanced Data Security
Data security is crucial in fraud detection to protect sensitive customer information and prevent unauthorized access. Implement robust security measures such as encryption, access controls, and regular security audits to ensure data protection and maintain regulatory compliance.
Elevate Your Banking Security with Data Modernization, Want to know how? We are here to help you.
Methods to consider while enhancing the data security of the banking network:
1. Encryption: Encryption is a fundamental technique used to protect data by converting it into an unreadable format using encryption algorithms. Strong encryption methods, such as Advanced Encryption Standard (AES), are employed to ensure the confidentiality and integrity of sensitive information.
2. Access Controls: This involves using techniques such as strong passwords, multi-factor authentication (MFA), role-based access controls (RBAC), and privileged access management (PAM) to limit access to data based on user roles and responsibilities.
3. Data Classification: By classifying data into different tiers, such as public, internal, confidential, or highly sensitive, organizations can implement targeted security measures to protect the most critical data.
4. Data Loss Prevention (DLP): DLP solutions use a combination of content analysis, keyword matching, and data fingerprinting to detect and prevent data breaches. They can monitor data in various forms, such as emails, files, and network traffic, and enforce policies to prevent data exfiltration.
5. Secure Data Transmission: Secure communication protocols, such as HTTPS (HTTP over SSL/TLS), are used to encrypt data during transmission, preventing unauthorized interception and tampering.
Virtual Private Networks (VPNs) can also be employed to create secure connections between users and the network, especially when accessing data remotely.
6. Data Backup and Recovery: Enhanced data security involves regular data backups and establishing robust disaster recovery plans.
7. Employee Awareness and Training: Employees play a critical role in data security. Regular training sessions and simulated phishing exercises help educate employees and promote a security-conscious culture.
8. Compliance with Data Protection Regulations: Enhanced data security assures adherence to pertinent data protection laws and standards, such as the General Data Protection Regulation (GDPR), Payment Card Industry and the Data Security Standard, along with the Health Insurance Portability and Accountability Act (HIPAA).
5. Going an extra mile: Some other methods for improved security
1. Collaboration and Information Sharing
Collaboration and information sharing refer to the practices and processes of sharing knowledge, data, and insights among individuals, teams, departments, or organizations. It involves the exchange of information, ideas, and resources to foster collaboration, enhance decision-making, and improve overall productivity and effectiveness.
It can extend to the sharing of data and analytics insights. Organizations can share data sets, analytical models, and best practices to drive data-driven decision-making and improve overall business performance.
2. Continuous Monitoring and Adaptive Controls
Continuous monitoring and adaptive controls are key components of an effective risk management and security strategy. They involve ongoing monitoring of systems, networks, and processes, as well as the implementation of dynamic controls that adapt to changing threats and risks.
Continuous monitoring is often facilitated using automated monitoring tools and security information and event management (SIEM) systems. These tools collect and analyze security logs, network traffic, system events, and other relevant data to detect and alert to potential security incidents. Automated monitoring enhances efficiency, reduces manual efforts, and enables timely detection of security threats.
By establishing a proactive and dynamic security approach, organizations can detect and respond to security incidents in real time, adapt their security controls to changing conditions, and effectively mitigate risks to their systems, data, and operations.
3. Regular Assessment and Improvement
Continuously evaluate the effectiveness of fraud detection strategies and adapt them as fraud techniques evolve. Stay informed about the latest advancements in fraud detection technologies and explore opportunities to leverage emerging technologies such as blockchain, big data analytics, and cloud computing.
Regular assessment and improvement are essential for organizations to adapt to changing business environments, enhance operational efficiency, and stay ahead of competitors. By consistently evaluating performance, identifying areas for improvement, and implementing necessary changes, organizations can optimize their processes, enhance customer satisfaction, and achieve sustainable growth.
Looking to Secure Your Banking Operations, and what to know Data Modernization Strategies can help you.
Conclusion
Implementing the above data modernization strategies can significantly enhance a bank’s fraud detection capabilities, helping to protect customers and minimize financial losses due to fraudulent activities. However, it’s important to note that no strategy is foolproof, and banks should maintain a multi-layered approach to fraud prevention, combining technology, analytics, employee training, and customer education.
