- May 22, 2017
- Posted by: Abhay Das
- Category: Digital Assurance
What is WannaCry?
A worldwide cyber-attack has been happening since Friday, affecting more than 200,000+ organizations in 150+ countries.
The WANNACRY RANSOMWARE ATTACK has rapidly become the nastiest digital disaster to strike the internet, crippling transportation and hospitals globally. But, it progressively appears that it is not the work of hacker brains.
Instead, cyber-security detectives see the recent breakdown of cyber-criminal scheme, which reveals amateur mistakes made at every steps.
How does Ransomware Work?
Ransomware is a kind of cyber-attack, in which, hackers take control of a computer system and block access to it until a ransom is paid.
The cyber criminals need to download a type of malicious software onto a system within the network to gain access to the system. This is often done by making the victim click on a link or download it by mistake.
Once the software gets into the victim’s computer, the hackers can launch an attack that will lock all the files it finds within the network. It tends to be a gradual process with files being encrypted one after the other.
Though the infection stage is somewhat different for each Ransomware version, the key stages are as follows:
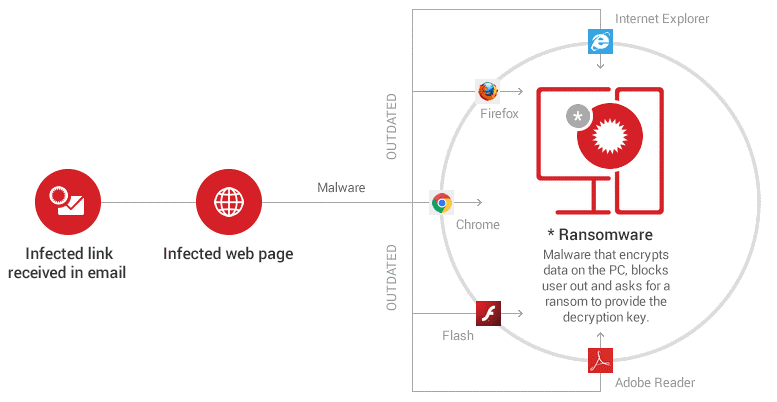
- Initially, the victim gets an email that includes a malicious link or a malware attachment. Alternatively, the contagion can originate from a malicious website that delivers a security exploit to create a backdoor on the victim’s PC by using a susceptible software from the system.
- If the victim clicks on the link or downloads and opens the attachment, a downloader (payload) will be placed on the affected PC.
- The downloader uses a list of domains or C&C servers to download the Ransomware program on the system.
- The contacted C&C server responds by sending back the requested data.
- The malware then encrypts the entire hard disk content, personal files, and sensitive information. Everything, including data stored in cloud accounts (Google Drive, Dropbox) synced on the PC is encrypted by the malware. It can also encrypt data on other computers connected to the local network.
- Then a warning pops up on the screen with instructions on how to pay for the decryption key.
Taking Ransomware Protection to Next Level
One should take the threat of Ransomware seriously and do something about it before it smashes the data.
Here are few precautions to
Local PC:
Step 1: Do not store important data only on your PC. Take 2 backups of data: on an external hard drive and in the cloud – Dropbox/Google Drive/etc.
Step 2: The Dropbox/Google Drive/OneDrive/ applications should not be turned on by default.
Step 3: Turn off macros in the Microsoft Office suite – Word, Excel, PowerPoint, etc.
In the browser:
- Block and set the plugins to ask for permissions for the following plugins from the browser: Adobe Flash, Adobe Reader, Java and Silverlight and activate the plugins when needed.
- Adjust the browsers’ security and privacy settings for increased protection.
- Update all outdated plugins and add-ons from my browsers.
- Use an ad-blocker to avoid the threat of potentially malicious ads.
Online Behaviour:
- Never open spam emails or emails from unknown senders.
- Never download attachments from spam emails or suspicious emails.
- Never click links in spam emails or suspicious emails.
- Use Anti-ransomware security tools such as Norton, Bitdefender, Kaspersky, Trend Micro Internet Security, Zemana Anti-malware.
- Use a reliable, paid antivirus product that includes an automatic update module and a real-time scanner.
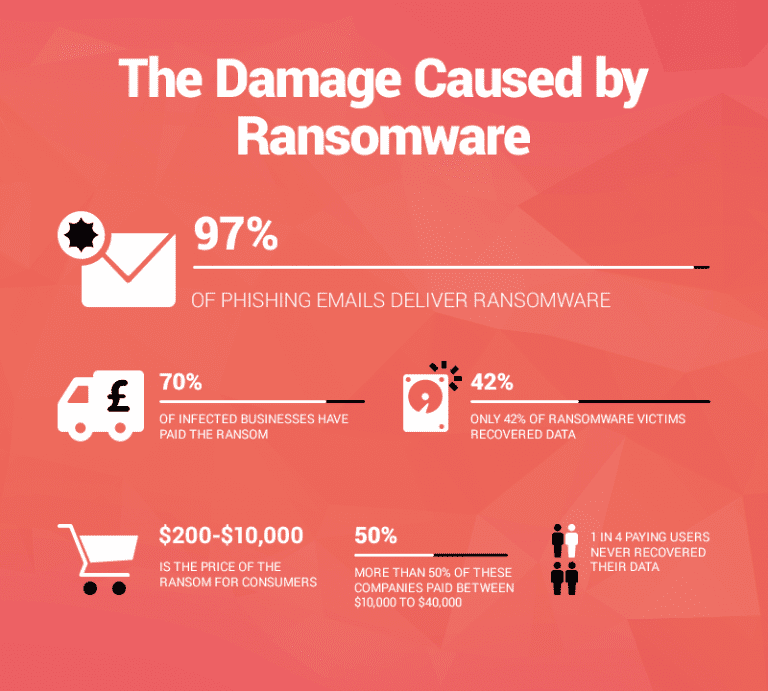
“Should I pay the ransom or not?”
The answer is a big NO.
Paying the ransom does not give guarantee that the online criminals at the other end of the Bitcoin transfer will give the decryption key. And even if they do, there will be further greedy attacks, which will become a never-ending malicious cycle of cyber-crime.
Putting things into perspective, 1 out of every 4 cyber-crime victim who paid the ransom didn’t get their data back. They lost both the information and their money.
How to get the data back without paying the ransom?
There are many versions and types of Ransomware, but cyber security researchers are working round the clock to break the encryption that at least some of them use. There are many other cryptoware strains that are well coded and only specialists are able to crack.
Not sure if your system in secure? Don’t Worry!!
Our Security Testing experts will guide You
To recover the data without funding Ransomware creators, we have put together a significant list of Ransomware decryption tools which can be used.
| OpenToYou Globe3 decryption tool Dharma Decryptor CryptON Alcatraz HiddenTear NoobCrypt CryptoMix/CryptoShield decryptor Damage ransomware .777 ransomware 7even-HONE$T .8lock8 ransomware decrypting tool 7ev3n decrypting tool Agent.iih Alma decrypting tool Al-Namrood Alpha AlphaLocker Apocalypse ApocalypseVM Aura AutoIt Autolocky Badblock Bart decrypting tool BitCryptor BitStak Chimera CoinVault Cryaki Crybola CrypBoss Crypren | Crypt38 Crypt888 CryptInfinite CryptoDefense CryptoHost Cryptokluchen CryptoTorLocker CryptXXX CrySIS decrypting tool CTB-Locker Web CuteRansomware DeCrypt Protect Democry decrypting tool DMA Locker decrypting tool + DMA2 Locker decoding tool Fabiansomware FenixLocker Fury decrypting tool GhostCrypt decrypting tool Globe / Purge Gomasom Harasom HydraCrypt Jigsaw/CryptoHit KeRanger KeyBTC KimcilWare Lamer decrypting tool LeChiffre Legion Linux.Encoder Lock Screen ransomware Locker Lortok | MarsJoke Manamecrypt Mircop decrypting tool + alternative Merry Christmas / MRCR decryptor Nanolocker Nemucod NMoreira ransomware ODCODC Operation Global III Ransomware Ozozalocker ranomware decryptor PClock Petya Philadelphia PizzaCrypts Pletor Pompous PowerWare / PoshCoder Radamant Rakhni Rannoh Rector Rotor Scraper Shade / Troldesh SNSLocker Stampado SZFlocker TeleCrypt TeslaCrypt TorrentLocker Umbrecrypt |
Please read about how these tools work before using it as a solution.
Do keep in mind that decryptors could become outdated due to constant updates and new versions released by cyber criminals. This is a never-ending battle, which is why we should focus on prevention and having multiple backups for your data.